This feature is only available for Devolutions Server, Microsoft Azure SQL, Microsoft SQL Server, and SQLite workspaces.
Multifactor authentication (MFA) identifies users by at least two different components: something that the user knows (often a password) and something that the user possesses (e.g., a validation code sent to a mobile device). If one of the components is missing or supplied incorrectly, the user's identity is not established with sufficient certainty and access to the workspace will remain blocked.
MFA is set at the workspace level, except in Devolutions Server, where it is set on the user. Remote Desktop Manager supports Authenticator (TOTP), Yubikey, and Duo.
Consult Lost the MFA set on the workspace in the the MFA has been lost.
In Remote Desktop Manager, go to the workspace for which you want to configure the MFA.
Go to File – My account settings and click on Workspace MFA.
In the Multifactor configuration window, click Change.
Select your MFA type in the drop-down list.
Follow one of the links below depending on the choice made in the previous step:
-
In Remote Desktop Manager, go to the workspace for which you want to configure the MFA.
-
Go to File – Workspaces and click on the Edit workspace button.
-
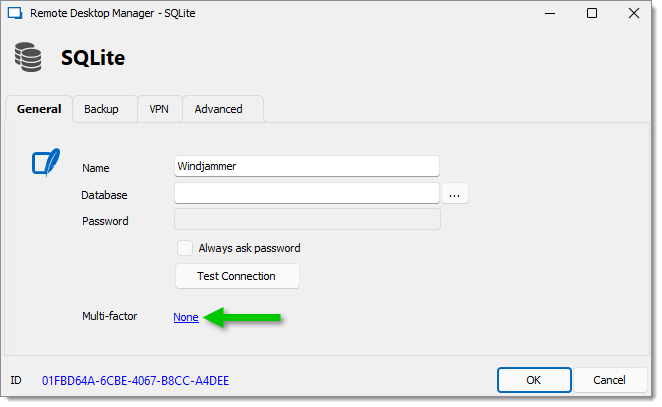
Next to the Multifactor option, click None.
-
In the Multifactor configuration window, click Change.
-
Select your MFA type in the drop-down list.
-
Follow one of the links below depending on the choice made in the previous step:
In the Devolutions Cloud web UI, head over to Administration – Authentication.
Toggle Enforce multi-factor verification on Devolutions Account. Doing so will force you to set up an MFA as well.
As mentionned before, multifactor authentication is set on a per-user basis for Devolutions Server workspaces. Here's how do to so:
Open the Devolutions Server web UI.
Go to Administration – Users, and Edit the user you wish to enforce MFA on.
In the Multi-factor tab, select Authenticator (TOTP). Changing the multifactor authentication of an administrator account requires entering its password.
Scan the QR code with your mobile app or use the key and account name to set up your account. Alternatively, you can check the Configure later by the user to leave those steps to the user.
Then, enter the code obtained by scanning the QR code.
Click Update to apply the changes to the user.
In Remote Desktop Manager, go to the workspace for which you want to configure the MFA.
Go to File – My account settings and click on Workspace MFA.
In the Multifactor configuration window, click Change.
Select your MFA type in the drop-down list.
Follow one of the links below depending on the choice made in the previous step:
In Remote Desktop Manager, go to the workspace for which you want to configure the MFA.
Go to File – Workspaces and click on the Edit workspace button.
Next to the Multifactor option, click None.
In the Multifactor configuration window, click Change.
Select your MFA type in the drop-down list.
Follow one of the links below depending on the choice made in the previous step:
In the Devolutions Cloud web UI, head over to Administration – Authentication.
Toggle Enforce multi-factor verification on Devolutions Account. Doing so will force you to set up an MFA as well.
As mentionned before, multifactor authentication is set on a per-user basis for Devolutions Server workspaces. Here's how do to so:
Open the Devolutions Server web UI.
Go to Administration – Users, and Edit the user you wish to enforce MFA on.
In the Multi-factor tab, select Authenticator (TOTP). Changing the multifactor authentication of an administrator account requires entering its password.
Scan the QR code with your mobile app or use the key and account name to set up your account. Alternatively, you can check the Configure later by the user to leave those steps to the user.
Then, enter the code obtained by scanning the QR code.
Click Update to apply the changes to the user.