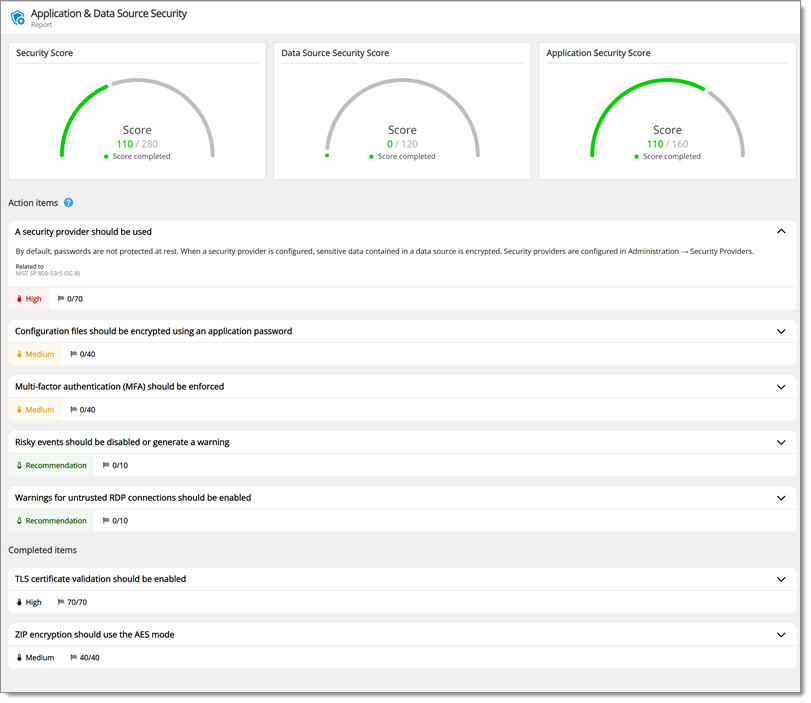
The Security dashboard is a tool to offer guidance on how to improve the security of the Devolutions Server platform and also tips on reducing the workload for administrators. Some tips are common infosec best practices, others are a consensus between our owns teams.
The scores are admittedly open to question and we do not pretend each topic has the same relative value for all of our community members. Achieving 100% is surely not an end goal in itself, we simply aim to raise awareness and provide ideas for your own security hardening. 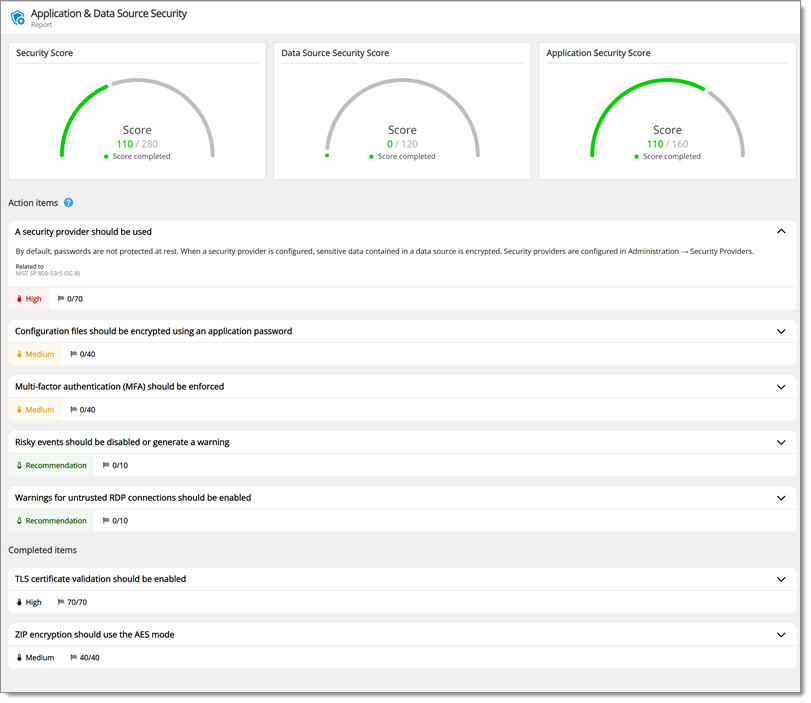
| |
|
| Description |
The LDAPS protocol should be used to provide communication confidentiality and integrity over the network. Otherwise, actions such as password resets could send the password in cleartext over the network. |
| Mitigation |
In the web interface Administration – Server Settings – Authentication – Domain, check Enable LDAPS. |
| |
|
| Description |
Backups should be configured to an external media or cloud storage to avoid permanent loss of data. |
| |
|
| Description |
Minimum privileges should be granted and applied for service and database accounts to operate. Shared and excessively privileged service and database accounts may induce unnecessary security risk exposure. |
| |
|
| Description |
An email server configuration is required to transmit important application messages such as security events or errors. |
| Mitigation |
Email server settings are in the web interface Administration – Server Settings – Email. |
| |
|
| Description |
Sending logs to an external system is recommended to maintain integrity and availability of event information. |
| Mitigation |
Logging is configured in the web interface Administration – Server Settings – Logging. |
| |
|
| Description |
Secure communications guarantee the integrity and confidentiality of the data transmitted between the client and the server. |
| |
|
| Description |
Excessive session duration may allow exposure beyond necessary to unauthorized users. Refresh token lifetime should therefore be configured within 24 hours (1440 min). |
| |
|
| Description |
Limiting the number of active administrators within the platform will reduce the attack surface of an attacker to only those accounts configured. Having more than 5 administrators can also be a sign of poor segregation of duty within the business unit or organization. |
| |
|
| Description |
The default MSSQL administrative account is a high privilege account that should only be used to manage the database instance. A less privileged user or service account is preferred to reduce impact of compromise. |
| |
|
| Description |
Sensitive information is stored in the server configuration file (appsettings.json). It is recommended to enable encryption to prevent tampering and ensure confidentiality |
| |
|
| Description |
Vault security level should be set to high in the vault settings. A high-level security vault does not have access to offline mode. |
| Mitigation |
Vault settings are in the web interface of Devolutions Server under Administration – User and Security Management – Vaults. Edit a vault to open the Edit vault settings window and select High in the drop-down menu under General – Security level. |
Devolutions Academy – Configuration and security