Encryption keys are used to encrypt data entries (connections, user vault, documentation, and attachments). They are generated and stored in the encryption.config file on the server only. To encrypt the data stored in the database, we use our open-source cryptography library.
We recommend doing a backup of the SQL database before any operation that could modify the information it contains (Import or Regenerate). During this operation, all users must be in offline mode or disconnected from the Devolutions Server data source to avoid data loss.
The encryption.config file cannot be moved directly to another system. It is encrypted using the data protection API (DPAPI), which binds the file to the system where it was originally encrypted. As a result, the file cannot be read or used on a different machine.
To use the encryption configuration on another system, you must export the encryption keys from the original system and then import them on the target system.
The same encryption keys must be used by all Devolutions Server instances in a high availability or load balancing topology that share the same SQL database. The same requirement also applies when performing a migration.
-
Open the Devolutions Server Console.
-
In the Tools tab, click on Export.

Tools – Export -
Enter a destination Filename and path, then set a password to protect the file.
We strongly recommend storing the encryption keys file in a secure storage outside of Devolutions Server such as Devolutions Hub Business, Azure Key Vault, or AWS Key Management Service.

Select a filename and set a password -
Click Ok.
Your encryption keys have been exported to the specified destination.
-
Open the Devolutions Server Console on the server.
-
In the Tools tab, click on Import.

Tools – Import -
Select the encryption keys file, then enter the password.

Select the file and enter the password -
Click Ok.
Once the operation is complete, the new encryption keys are applied to the data in the database.
Regenerating encryption keys modifies and re-encrypts the data stored in the Devolutions Server SQL database. This operation must be performed with the utmost care.
There may be situations where you need to regenerate the encryption keys, for example if you suspect that your database has been compromised. The following steps explain how to perform this operation.
-
Create a full backup of the database and ensure that the backup is valid and usable.
-
Back up the Devolutions Server web application folder.
-
Export the existing encryption keys. See the export procedure in this page.
-
In the Server tab, switch the Devolutions Server instance to offline mode by clicking Go offline.
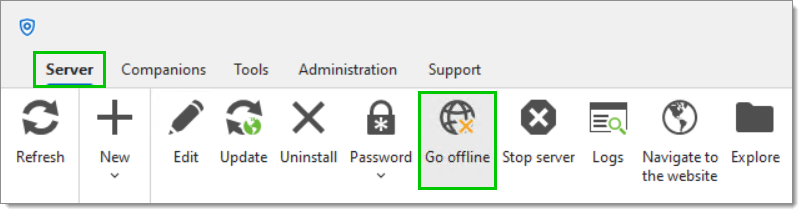
Server – Go offline -
Go to the Tools tab and click on Regenerate.

Tools – Regenerate -
Enter a destination Filename and path, then set a password to protect the file.
We strongly recommend storing the encryption keys file in a secure storage outside of Devolutions Server such as Devolutions Hub Business, Azure Key Vault, or AWS Key Management Service.
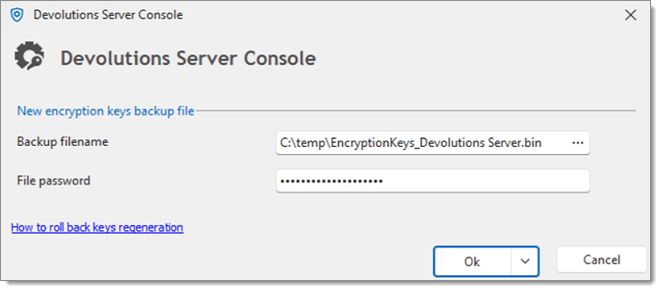
Select a filename and set a password -
Click Ok.
-
A final warning appears before the regeneration process begins. Click OK again to proceed.

Confirm the encryption keys regeneration
The regeneration process will start. Once completed, the status will indicate that the operation has finished.
If errors occur during the regeneration process, follow these instructions to restore the Devolutions Server instance to its previous state:
Restore your database to the backup taken just prior to the key regeneration.
Navigate to the
App_Datafolder at the root of your Devolutions Server instance.Rename the
encryption.configfile toencryption.config.bak(Devolutions Server will now ignore this file).Rename the most recent
encryption.<date and time>.configfile toencryption.config.Restart the application pool if needed.