Devolutions Server allows account passwords rotation by using an Active Directory account as a PAM provider. This article describes the steps to delegate control to said PAM provider in the Active Directory Users and Computers console.
To manage domain administrator accounts as privileged accounts in the PAM module, grant the PAM AD provider account access to the AdminSDHolder. See Creating Management Accounts for Protected Accounts and Groups in Active Directory for step-by-step instructions.
Open the Active Directory Users and Computers console.
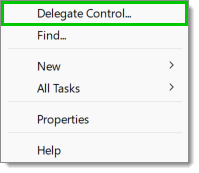
Right-click on the Organizational Unit (OU) containing the privileged accounts or a higher OU level to encompass all OUs in which the PAM provider account should have the ability to rotate account passwords, and select Delegate Control....
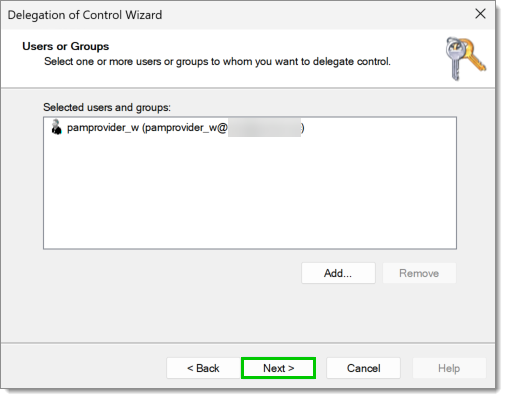
In the Delegation of Control Wizard, click on Next to reach the Users or Groups dialog. There, choose the account to use as the PAM provider account in Devolutions Server before clicking on Next.
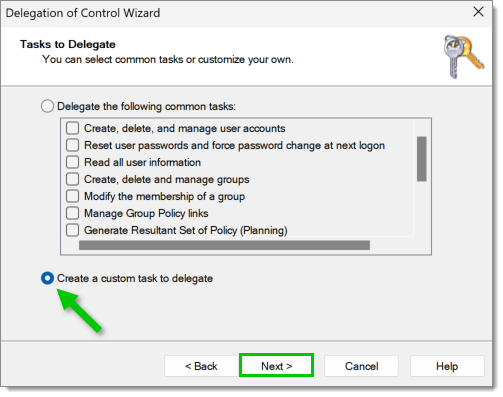
In Tasks to Delegate, select Create a custom task to delegate, and click on Next..
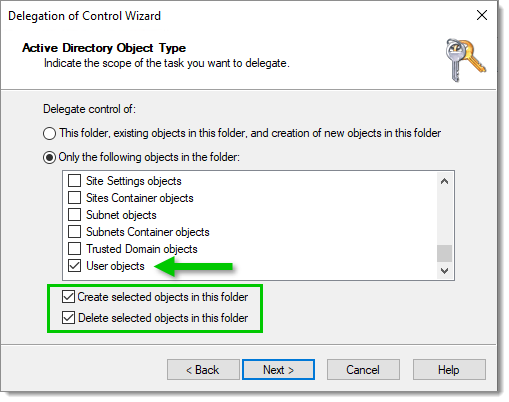
In Active Directory Object Type, select the Only the following objects in the folder option, and check the User objects item. Then click Next.
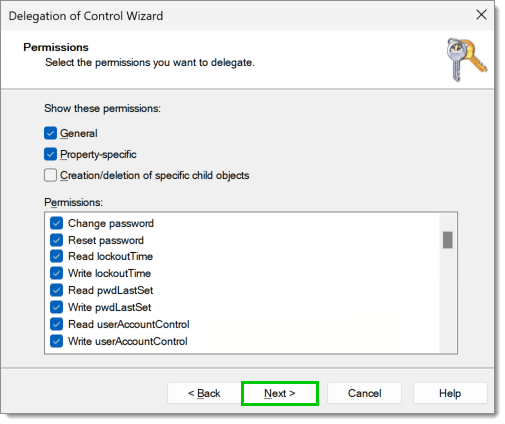
In Permissions, show General and Property-specific permissions, and check the following items before clicking on Next:
Change password
Reset password
Read lockout Time
Write lockout Time
Read pwdLastSet
Write PwdLastSet
Read userAccountControl
Write userAccountControl
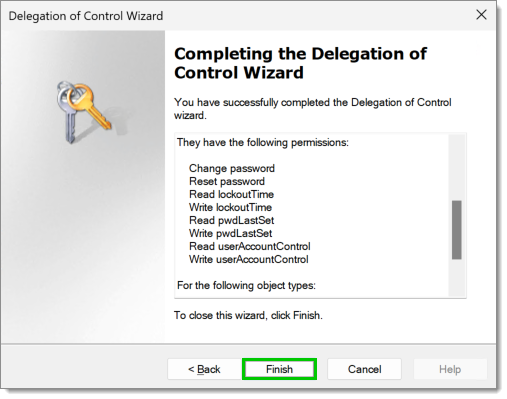
Review the changes as neccessary and click on the Finish button to complete delegating control.
The password rotation feature will use the default built-in Devolutions Server password rules. To level up the password rules to respect domain password rules, create a password template in Administration – Password templates, then set it as the default password template in Administration – System settings – Password management – Password template.






